Hello guys,
I have had a ticket for a long time, which I was finally able to solve.
The screenshots are from my test lab. The log entries are partially anonymised.
The problem
The problem was that a customer wanted to use AD SSO in his secondary location. The secondary location has a RODC. During the setup, we encountered the problem that the proxy did not recognise which AD group the test user was in. As a result, the proxy rules that worked on the basis of AD groups did not apply.
Log entry
2020:12:02-17:00:13 Test-UTM httpproxy[6301]: id="0003" severity="info" sys="SecureWeb" sub="http" name="http access" action="pass" method="GET" srcip="192.168.88.12" dstip="" user="testuser" group="" ad_domain="SPDNS"
As you can see in the entry, the user and the domain are recognised. However, not the group.
what have we check
UTM configuration
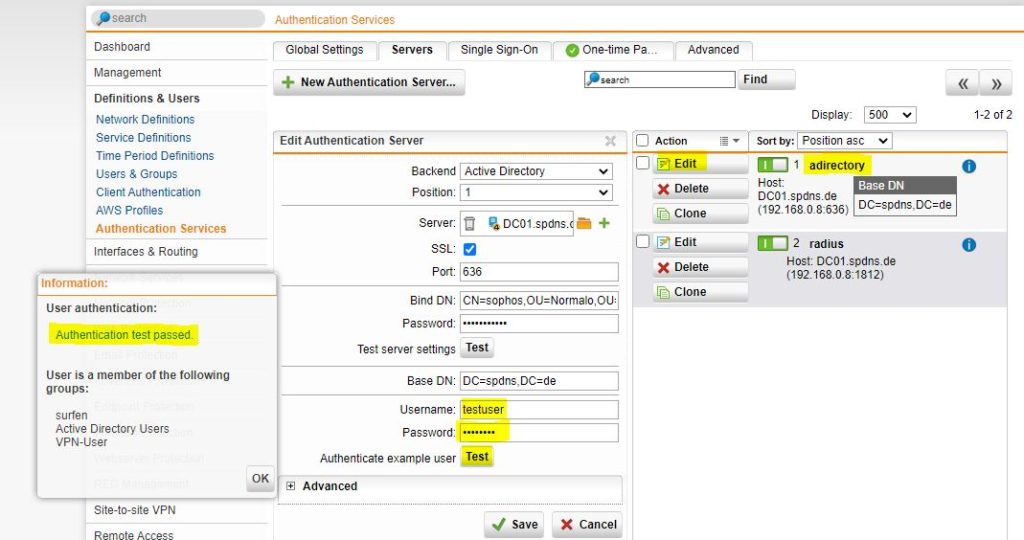
First we checked whether the utm can authenticate the user against the AD.
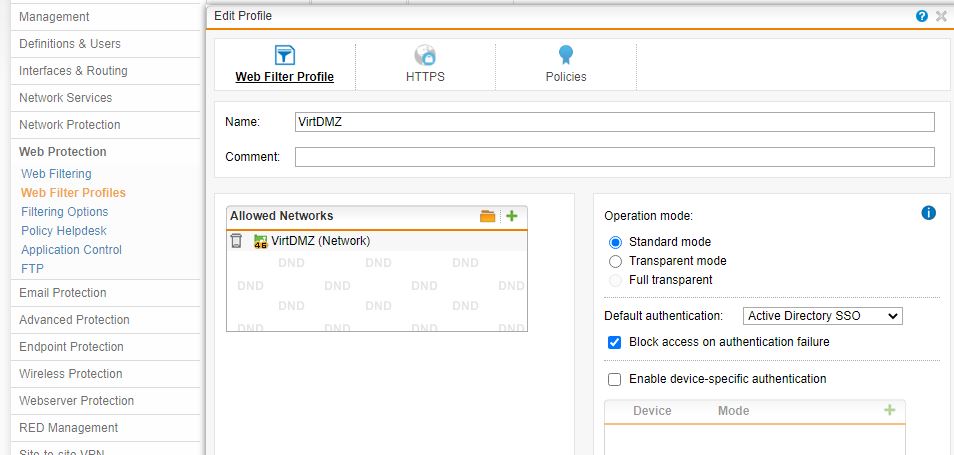
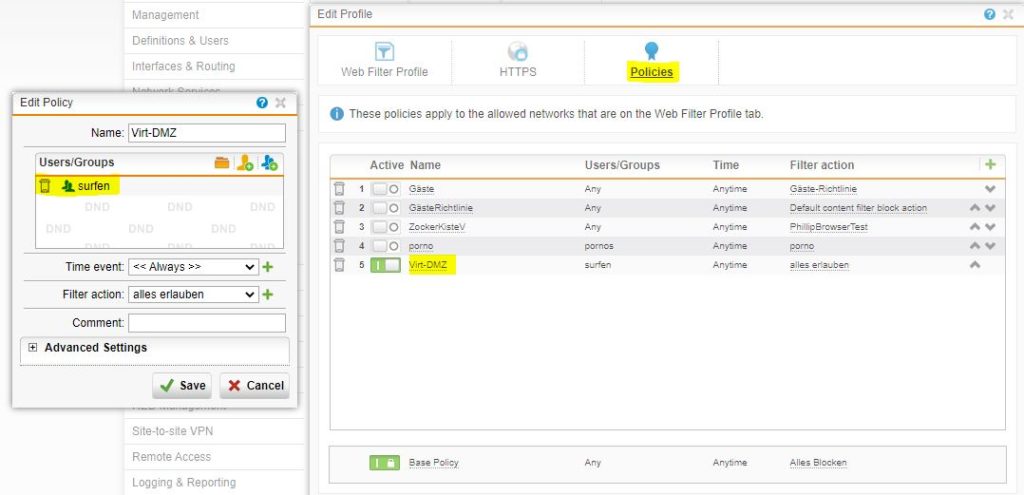
Now we took a closer look at the proxy configuration.
The group “surfen”, is a imported AD group. You can the this by the user authentication test screenshot.
All OK.
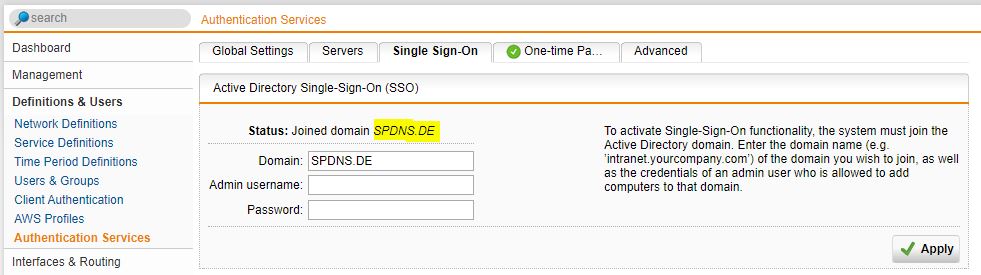
As the last step on the UTM, I checked the AD SSO status.
On the RODC
The UTM had a computer account and all was right.
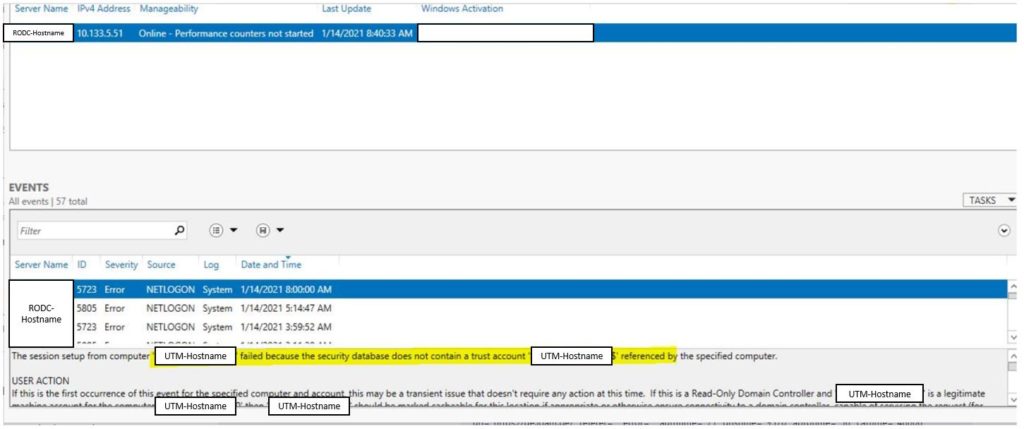
By chance I came across a netlogon error message in the server manager.
After deleting the UTM computer account in the AD and a rejoin, it worked. :D
I suspect that something didn’t work right the first time I joined the AD. And the second time it finally worked.
Have a nice day!









2 Responses
Thanks for the nice explanation
Thanks for the nice comment