Group policy
There are several HowTos out there to publish the Internet Explorer via group policies but I had several problems with different domain controller OS versions and domain-levels. Newest group policies can’t provide support for the newest Internet Explorer so I found my way to configure all versions of Internet Explorer. We will configure the following registry-settings:
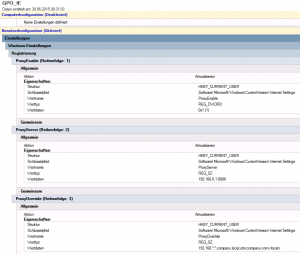
Windows Registry Editor Version 5.00 [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings] "ProxyEnable"=dword:00000001 "ProxyServer"="192.168.0.1:8080" "ProxyOverride"="192.168.*;*.company.local;utm.company.com;<local>"
Go to User-Configuration/Settings/Windows-Settings/Registry and configure this three registry-keys:
link the group-policy to your user OU and right-click the item. Click on “force” to set always these settings on the client.
WPAD
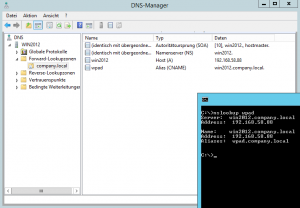
In a company where you have workers with mobile devices such as notebooks, you have a problem when they have a proxy configured in their browsers and move to home or public wifi network. The always need to deactivate it by hand. So how can we configure the proxy only when the worker connects to the office network? The solution is WPAD. Every computer asks the configured DNS server for the host entry “wpad”. So you need to configure a wpad CNAME pointing to your webserver that will host the wpad-file.
Since Windows Server 2008, the DNS server has a blocklist which contains isatap and wpad. So when you query the DNS server, you won’t get an IP address back. To change this, you need to change the RED_DWORD “EnableGlobalQueryBlockList” at “HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\DNS\Parameters” from 1 to 0. This action needs to be done on every DNS server. You can also spread this reg-key via group policy.
The CNAME entry will look like this:
You can now install or use the webserver to provide access to the wpad-file. I’m using Microsoft IIS. After the installation, you can create a file called “wpad.dat” in C:\inetpub\wwwroot with the following content:
function FindProxyForURL(url, host) {
if (isPlainHostName(host)) {return "DIRECT"; }
if (shExpMatch(url,"*.domain.local/*")) { return "DIRECT"; }
if (shExpMatch(url,"another url*")) { return "DIRECT"; }
if (isInNet(host, "127.0.0.0", "255.0.0.0")) { return "DIRECT"; }
if (isInNet(host, "10.0.0.0", "255.0.0.0")) { return "DIRECT"; }
if (isInNet(host, "172.16.0.0", "255.240.0.0")) { return "DIRECT"; }
if (isInNet(host, "192.168.0.0", "255.255.0.0")) { return "DIRECT"; }
if (isInNet(myIpAddress(), "10.242.2.0", "255.255.255.0")) { return "DIRECT"; }
return "PROXY hostname-of-utm(or IP address):8080; DIRECT";
}
Keep in mind: When u are using a DNS hostname, the client talks “kerberos” to the proxy, if you are using an IP address, the browser will use NTLM. Some tools can’t handle kerberos. In this case, use the IP address of your proxy. The parameter with “myIpAddress” is the SSL VPN pool, so all connected clients won’t use the proxy.
You can also distribute WPAD information over DHCP leases (option 252) but there are servers etc. that don’t get an IP address from the DHCP server so I think the DNS entry is the better way.
Other browsers like Mozilla Firefox, Google Chrome or Opera are using “system settings” which are the configured Interet Explorer settings.









One Response